1Password is looking to a password-free future. Here’s why
With phishing-based credentials theft on the rise, 1Password CPO Steve Won explains why the endgame is to 'eliminate’ passwords entirely.
Many software companies rely on open-source code but lack consistency in how they measure and handle risks and vulnerabilities associated with open-source software, according to a new report.
Looking for the best payroll software for your small business? Check out our top picks for 2023 and read our in-depth analysis.
What's the best project management software for Mac users? Use our in-depth guide to learn more about pricing, standout features and more.
Whether you're starting a new business venture and need Microsoft Office's help or you just want to get better organized in your personal life, it's a good time to take advantage of this limited-time deal.
Looking for the right password management fit for your organization? These eight options all have something to offer, and one may be the best fit for you.
Organize a number of different applicants using an ATS to cut down on the amount of unnecessary time spent finding the right candidate.
Antivirus software protects your data against cybercriminals, ransomware and malware. Compare the best software now.
VPNs are an essential component in small and medium-sized businesses' cybersecurity toolkit. Here's how leading VPN services for SMBs compare.

Process mining is a data science and process management technique that's evolving with digital transformation business projects. Learn how process mining is impacting modern enterprises and business resilience goals.
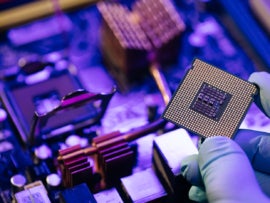
If the U.S. is to move chip manufacturing back within its borders, more talent will be needed to meet domestic demand — even for just critical applications.

Learn what change data capture is, why it exists and how to use it to maintain a historical record of changes to your database.

AR and VR development has gathered a lot of momentum in recent years. With 5G offering improved capabilities in network connectivity, how can AR and VR tap into these capabilities?

Learn some of today's most popular attacks and how to mitigate them with The All-in-One Ethical Hacking & Penetration Testing Bundle.

Taskade makes it very easy to manage a list of tasks for small and mid-sized projects. Find out how to add a kanban-like board to your Workspace to make things even easier.

This policy outlines the measures the organization is taking to ensure protection of its confidential information, including the imposition of a contractual obligation in the form of a nondisclosure agreement. From the policy: SUMMARY A nondisclosure policy protects an organization’s confidential information from exposure to persons outside or inside the organization who could intentionally or ...

Maintenance tasks, equipment upgrades and installations must be completed regularly — potentially creating disruptions and preventing employees from doing their work. This policy is designed to help your organization determine procedures for scheduling and communicating server, system and network downtime with the goal of minimizing the impact and inconvenience for your staff, clients and contractors. ...

With Azure AD and FIDO security keys, you can make MFA more secure and avoid having to provision certificates on everyone’s phones.

Work from anywhere while still being able to view and use your laptop and smartphone hands-free with the Aduro U-Rise Duo — now 65% off.